- Home
- People
- Projects
- Practical Security Verification
- Secure Cloud Computing
- Security of AI Systems
- Deep Learning for Security
- Smartphone Security
- Cache Side-Channels and Secure Caches
- De-anonymization
- Running Unvetted Programs
- Secure RISC-V processor
- SP and Bastion Secure Processor Architectures
- Crypto Acceleration
- OpenSPARC Researh
- SecureCore
- Advanced Bit Manipulation
- PAX
- PLX
- Publications
- Research
- Conference and Journals
- Project Archive
- Photos
Secure Cloud Computing
A list of PALMS papers related to cloud computing
A. Overall Architecture
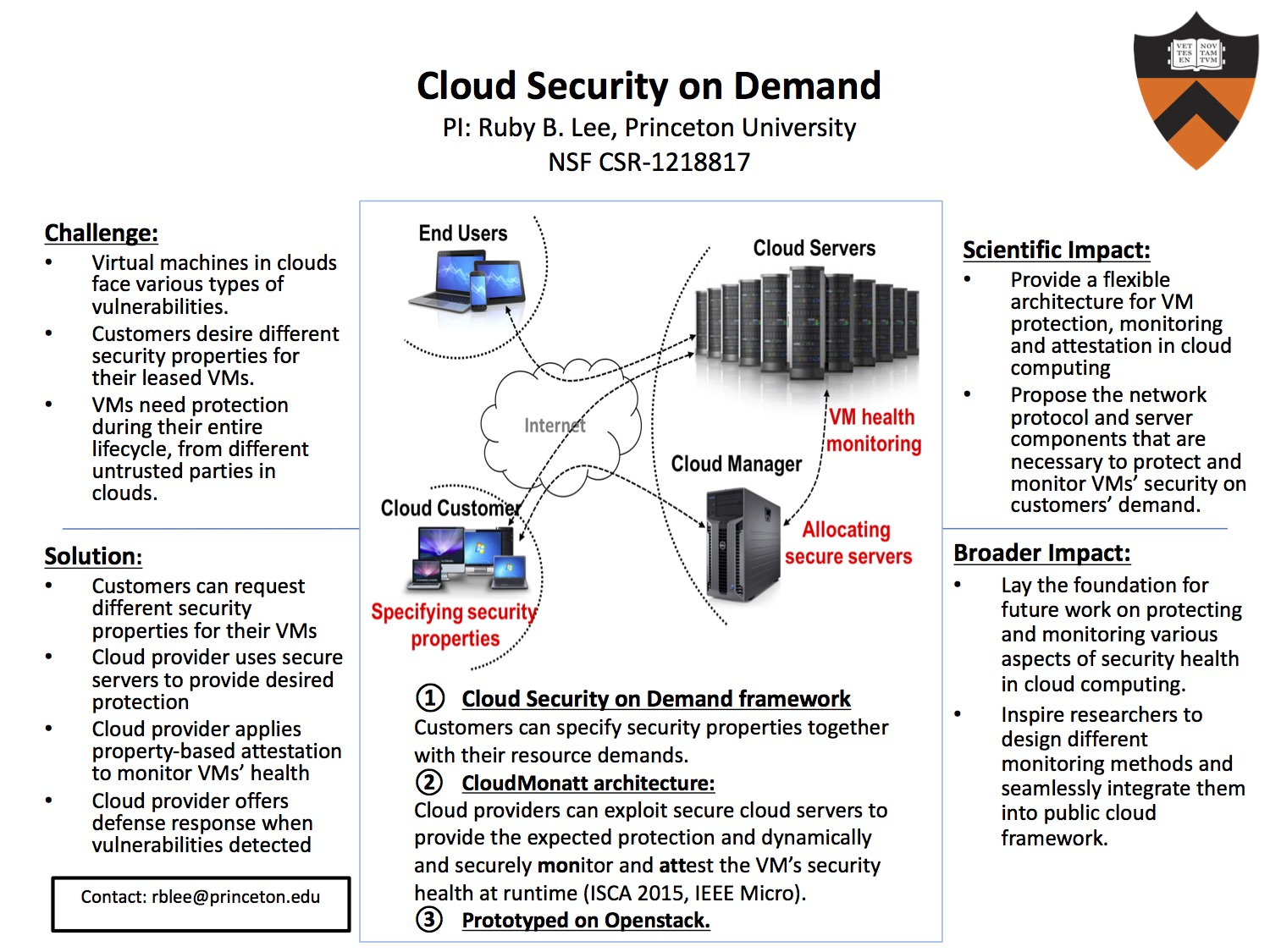
1. Cloud Security on Demand
We present our vision for Security on Demand in cloud computing: a system where cloud providers can offer customized security for customers’ code and data throughout the term of contract. Security on demand enables security-focussed competitive service differentiation and pricing, based on a threat model that matches the customer’s security requirements for the virtual machine he is leasing. It also enables a cloud provider to bring in new secure servers to the data center, and derive revenue from these servers, while still using existing servers. We propose a mechanism for requesting different types of VM security based on different underlying threat models. Then we define a detailed mapping of security features expected by customers to a set of threat models, and then to secure server architectures. We propose a mechanism for managing trust in the cloud servers based on the hardware and/or software security mechanisms they provide. We show a prototype implementation of the above features within the opensource OpenStack cloud software.
- Pramod Jamkhedkar, Jakub Szefer, Diego Perez-Botero, Tianwei Zhang, Gina Triolo and Ruby B. Lee, " A Framework for Realizing Security on Demand in Cloud Computing", in IEEE International Conference on Cloud Computing Technology and Science (CloudCom), 2013. [code]
2. CloudMonatt: Monitoring and Attestation of Virtual Machines’ Security Health
Cloud customers need guarantees regarding the security of their virtual machines (VMs), operating within an Infrastructure as a Service (IaaS) cloud system. This is complicated by the customer not knowing where his VM is executing, and on the semantic gap between what the customer wants to know versus what can be measured in the cloud. We present an architecture for monitoring a VM’s security health, with the ability to attest this to the customer in an unforgeable manner. We show a concrete implementation of property-based attestation and a full prototype based on the OpenStack open source cloud software. We use some concrete examples to show how to bridge the semantic gap between security properties and measurements, e.g., VM integrity, runtime confidentiality through covert channels, runtime CPU availability.
- Tianwei Zhang and Ruby B. Lee " Monitoring and Attestation of Virtual Machine Security Health in Cloud Computing". IEEE Micro Special Issues on Security, Volume 36, Issue 5, 2016
- Tianwei Zhang and Ruby B. Lee, " CloudMonatt: an Architecture for Security Health Monitoring and Attestation of Virtual Machines in Cloud Computing". In ACM International Symposium on Computer Architecture (ISCA), 2015. [code]
B. Virtualization Protection
3. NoHype: Hypervisor Free Virtualization
Cloud computing is a disruptive trend that is changing the way we use computers and virtualization is the key underlying technology in cloud infrastructures. Unfortunately, the use of virtualization is the source of a significant security concern: multiple virtual machines (VMs) run on the same server and since the virtualization layer plays a considerable role in the operation of a virtual machine, a malicious VM has the opportunity to attack the virtualization layer. A successful attack would give the malicious VM control over the all-powerful virtualization layer and potentially compromise the confidentiality and integrity of the virtualization layer and the other VMs. The NoHype system architecture proposes removing the virtualization layer while retaining the key features needed to be able to provide for multi tenancy of VMs. The NoHype architecture is named to indicate the removal of the hypervisor (no hypervisor) but we also try to show that the NoHype architecture may indeed be implementable on today's commodity hardware (not a hype). By removing bulky virtualization layer we propose that the architecture improves security while retaining key functionality to be able to host multiple VMs on same physical hardware.
- Eric Keller, Jakub Szefer, Jennifer Rexford, and Ruby B. Lee, "NoHype: Virtualized cloud infrastructure without the virtualization," in proceedings of the International Symposium on Computer Architecture (ISCA 2010), pages 350-357, June 2010.
- Jakub Szefer, Eric Keller, Ruby B. Lee and Jennifer Rexford, "Eliminating the Hypervisor Attack Surface for a More Secure Cloud," to appear in Proceedings of the Conference on Computer and Communications Security (CCS 2011), October 2011.
4. Hyperwall: Hypervisor-Secure Virtualization
Virtualization has become a standard part of many computer systems. A key part of virtualization is the all-powerful hypervisor which manages the physical platform and can access all of its resources, including memory assigned to the guest virtual machines (VMs). Continuing releases of bug reports and exploits in the virtualization software show that defending the hypervisor against attacks is very difficult. In this work, we present hypervisor-secure virtualization – a new research direction with the goal of protecting the guest VMs from an untrusted hypervisor. We also present the Hy- perWall architecture which achieves hypervisor-secure virtualization, using hardware to provide the protections. HyperWall allows a hypervisor to freely manage the memory, processor cores and other resources of a platform. Yet once VMs are created, our new Confidentiality and Integrity Protection (CIP) tables protect the memory of the guest VMs from accesses by the hypervisor or by DMA, depending on the customer’s specification. If a hypervisor does become compromised, e.g. by an attack from a malicious VM, it cannot be used in turn to attack other VMs. The protections are enabled through minimal modifications to the microprocessor and memory management units. Whereas much of the previous work concentrates on protecting the hypervisor from attacks by guest VMs, we tackle the problem of protecting the guest VMs from the hypervisor.
- Jakub Szefer and Ruby B. Lee, "Architectural Support for Hypervisor-Secure Virtualization," in Proceedings of the International Conference on Architectural Support for Programming Languages and Operating Systems (ASPLOS), March 3–7, 2012.
- Jakub Szefer and Ruby B. Lee, "A Case for Hardware Protection of Guest VMs from Compromised Hypervisors in Cloud Computing," in Proceedings of the Second International Workshop on Security and Privacy in Cloud Computing (SPCC), June 20-24, 2011.
5. Hypervisor Vulnerabilities
The rise of the Cloud Computing paradigm has led to security concerns, taking into account that resources are shared and mediated by a Hypervisor which may be targeted by rogue guest VMs and remote attackers. In order to better define the threats to which a cloud server’s Hypervisor is exposed, we conducted a thorough analysis of the codebase of two popular open-source Hypervisors, Xen and KVM, followed by an extensive study of the vulnerability reports associated with them. Based on our findings, we propose a characterization of Hypervisor Vulnerabilities comprised of three dimensions: the trigger source (i.e. where the attacker is located), the attack vector (i.e. the Hypervisor functionality that enables the security breach), and the attack target (i.e. the runtime domain that is compromised). This can be used to understand potential paths different attacks can take, and which vulnerabilities enable them. Moreover, most common paths can be discovered to learn where the defenses should be focused, or conversely, least common paths can be used to find yet-unexplored ways attackers may use to get into the system.
- Diego Perez-Botero, Jakub Szefer and Ruby B. Lee, "Characterizing Hypervisor Vulnerabilities in Cloud Computing Servers," in Proceedings of the Workshop on Security in Cloud Computing (SCC), 2013. [Database]
C. Virtual Machine Attacks and Defenses
6. Memory DoS attacks
In cloud computing, network Denial of Service (DoS) at- tacks are well studied and defenses have been implemented, but severe DoS attacks on a victim’s working memory by a single hostile VM are not well understood. Memory DoS attacks are Denial of Service (or Degradation of Service) at- tacks caused by contention for hardware memory resources on a cloud server. Despite the strong memory isolation techniques for virtual machines (VMs) enforced by the software virtualization layer in cloud servers, the underlying hardware memory layers are still shared by the VMs and can be exploited by a clever attacker in a hostile VM co-located on the same server as the victim VM, denying the victim the working memory he needs. In this project, we quantitatively explore the severity of contention on different memory resources. We show that a malicious cloud customer can mount low-cost attacks to cause severe performance degradation for a victim VM in public clouds. We design an effective, new defense against these memory DoS attacks, and implement a full prototype on the OpenStack cloud system.
- Tianwei Zhang, Yinqian Zhang and Ruby B. Lee, "Memory DoS Attacks in Multi-tenant Clouds: Severity and Mitigation," arXiv preprint 1603.03404v3, Oct 2017.
7. CloudRadar: A Real-Time Side-Channel Attack Detection System in Clouds
We present CloudRadar, a system to detect, and hence mitigate, cache-based side-channel attacks in multi-tenant cloud systems. CloudRadar operates by correlating two events: first, it exploits signature-based detection to identify when the protected virtual machine (VM) executes a cryptographic application; at the same time, it uses anomaly-based detection techniques to monitor the co-located VMs to identify abnormal cache behaviors that are typical during cache-based side-channel attacks. We show that correlation in the occurrence of these two events offer strong evidence of side-channel attacks. Compared to other work on side-channel defenses, CloudRadar has the following advantages: first, CloudRadar focuses on the root causes of cache-based side-channel attacks and hence is hard to evade using metamorphic attack code, while maintaining a low false positive rate. Second, CloudRadar is designed as a lightweight patch to existing cloud systems, which does not require new hardware support, or any hypervisor, operating system, application modifications. Third, CloudRadar provides real-time protection and can detect side-channel attacks within the order of milliseconds. We demonstrate a prototype implementation of CloudRadar in the OpenStack cloud framework. Our evaluation suggests CloudRadar achieves negligible performance overhead with high detection accuracy.
- Fangfei Liu, Yuval Yarom, Qian Ge, Gernot Heiser and Ruby B. Lee, "Last Level Cache Side-Channel Attacks are Practical," IEEE Symposium on Security and Privacy, 2015
- Fangfei Liu, Qian Ge, Yuval Yarom, Frank Mckeen, Carlos Rozas, Gernot Heiser, and Ruby B. Lee, "CATalyst: Defeating Last-Level Cache Side Channel Attacks in Cloud Computing," IEEE International Symposium on High Performance Computer Architecture, 2016
- Tianwei Zhang, Yinqian Zhang and Ruby B. Lee, "CloudRadar: A Real-Time Side-Channel Attack Detection System in Clouds," Research in Attacks, Intrusion and Defense, Sept. 2016
8. Pwnetizer: Fast VM Cloning
Availability is the one main security weaknesses of commodity Hypervisors. To address availability concern, we develop a new VM Cloning strategy. We focus on developing an efficient VM Cloning strategy for the creation of active VM clones. Our cloning technique provides us with several consistency and independence guarantees between the original VM and its clones: (1) main memory consistency at cloning time, independence after cloning; (2) persistent storage consistency at cloning time, independence after cloning; (3) no networking conflicts.
- Diego Perez-Botero, "Pwnetizer: Improving Availability in Cloud Computing Through Fast Cloning and I/O Randomization," MSE Thesis, Computer Science Department Department, Princeton University, Princeton, NJ, 2013.
9. Detecting VM-sourced network attacks
In this project, we aim to develop a method to detect network-based attacks from the source inside cloud systems.
D. Protecting from End-user Impersonation Attacks
- Wei-Han Lee, Ruby B. Lee, "Implicit Smartphone User Authentication with Sensors and Contextual Machine Learning," IEEE/IFIP International Conference on Dependable Systems and Networks, 2017
- Wei-Han Lee, Ruby B. Lee, "Implicit Authentication to Improve Smartphone Security," Springer Information Systems Security and Privacy. 576 160-176, 2016
- Wei-Han Lee, Ruby B. Lee, "Implicit Sensor-based Authentication of Smartphone Users with Smartwatch," Hardware and Architectural Support for Security and Privacy, 2016
- Wei-Han Lee, Ruby B. Lee, "Multi-sensor authentication to improve smartphone security," International Conference on Information Systems Security and Privacy, 2015. Nominated for Best Paper award.
E. Cloud Computing Benchmark Suites
PALMScloud Cloud Server Benchmarks
- Hao Wu, Fangfei Liu, Ruby B. Lee, "PALMScloud: Cloud Server Benchmark Suite for Evaluating New Hardware Architectures," IEEE Computer Architecture Letters. 15 (2), 2016
F. Other Papers
- Szefer, J., Lee, Ruby B. "Hardware-Enhanced Security for Cloud Computing," Secure Cloud Computing. Springer. New York. 57-76, 2014
- Szefer, J., Jamkhedkar, P., Perez-Botero, D., Lee, Ruby B, "Cyber Defenses for Physical Attacks and Insider Threats in Cloud Computing," ACM Symposium on Information, Computer and Communications Security (ASIACCS), 2014
- Jakub Szefer and Ruby B. Lee, BitDeposit: "Deterring Attacks and Abuses of Cloud Computing Services Through Economic Measures," Assured Cloud Computing workshop with IEEE/ACM International Symposium on Cluster, Cloud and Grid Computing, 2013
- Tianwei Zhang, Jakub Szefer and Ruby B. Lee, "Security Verification of Hardware-enabled Attestation Protocols," HASP, 2012
F. Thesis
- Tianwei Zhang. "Detection and Mitigation of Security Threats in Cloud Computing," PhD thesis, Princeton University, 2017
- Jakub Szefer. "Architectures for Secure Cloud Computing Servers ," PhD thesis, Princeton University, 2013
- Diego Perez-Botero. "Pwnetizer: Improving Availability in Cloud Computing Through Fast Cloning and I/O Randomization," MSE thesis, Princeton University, 2013
